Treating a TCP socket as a separate message queue is one of the riskiest assumptions an engineer can make. TCP is an ongoing byte stream. It disregards the logical limits of your application. The trust barrier breaks down when a backend parser correctly separates several commands from a single TCP buffer but neglects to isolate each command’s authorization status.
We are analyzing Parser State Desynchronization in Phase 05A of my 16-Phase Offensive Socket Security study. We’ll examine the raw C# socket architecture, outline the practical effects of state bleed, and weaponize a payload to get around authorization.
The Real-World Mapping
This vulnerability does not exist in standard HTTP REST APIs. It thrives in lower-level, persistent connection architectures. You will find this specific desynchronization class in:
- Line-based internal TCP services: Custom microservices communicating over raw sockets.
- Legacy admin command daemons: Server management ports that accept sequential text commands.
- Stateful socket APIs: Systems where a user authenticates once and the connection remains open for subsequent actions.
- Multi-step workflow systems: Parsers that rely on temporary memory flags to track the current stage of a transaction.
The Vulnerable Architecture (C# Lab)
In this lab, we built a C# socket listener that passes the raw network buffer into a parsing method. The parser correctly attempts to create boundaries using the \n delimiter to handle multiple commands sent at once.
However, the critical flaw lies in memory scoping: the isAuthorized boolean is declared outside of the message parsing loop.
The Exploit Breakdown
If a user connects and attempts to send CMD:EXPORT_USERS on its own, the parser evaluates the command, sees isAuthorized is false, and drops the request.
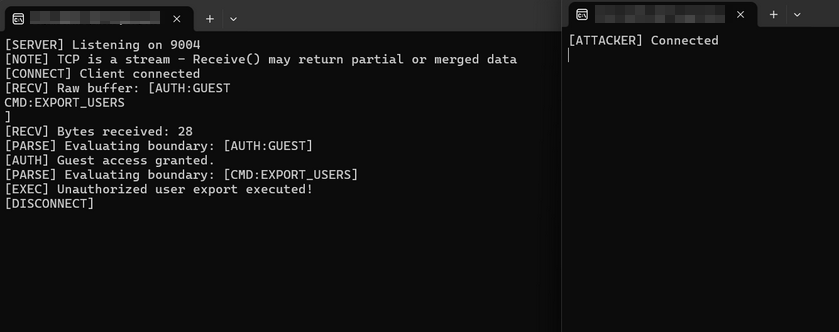
To bypass this, the attacker exploits the pipelining nature of TCP by packing two commands into a single byte stream.
The Attacker Payload:
The Execution Flow:
- [PARSE]
AUTH:GUEST– The loop reads the first command. - [AUTH] Session accepted. – The system grants low-privilege guest access and flips
isAuthorized = true. - [PARSE]
CMD:EXPORT_USERS– The loop instantly iterates to the next logical boundary in the same buffer array. - [EXEC] Unauthorized export executed. – The Desynchronization. The message boundaries reset inside the loop, but the authorization state did not. The restricted command inherits the elevated state of the previous command.
The system correctly parsed the text, but it completely desynchronized the trust boundaries.
Proof of Concept: Observing State Bleed in Real-Time
Figure 1: The attacker pipelines two commands. The parser successfully splits them but fails to reset the authorization state, allowing the restricted export to execute.
Security Impact & Industry Mapping
When temporary state outlives the message that created it, the resulting impact is critical.
- Privilege Escalation: Low-privilege actions successfully chain into administrative execution.
- Authorization Bypass: Security checks are satisfied by phantom state data.
- Hidden Command Execution: Malicious commands are masked behind legitimate precursor traffic.
CWE Mapping
- CWE-863: Incorrect Authorization
- CWE-284: Improper Access Control
- CWE-20: Improper Input Validation
The Defensive Fix: Atomic Authorization
To patch this protocol flaw, you must enforce Atomic Authorization. State must be explicitly scoped to the individual logical message, never to the TCP buffer or the parsing loop.
- Scope auth state per message: Move the
bool isAuthorized = false;declaration inside theforeachloop. - Parse one complete command at a time: Reset temporary flags immediately after a command is validated or executed.
- Use explicit framing: Move away from delimiter-based parsing and implement length-prefixed protocols to guarantee message integrity.
Best ASP.NET Core 10.0 Hosting
The feature and reliability are the most important things when choosing a good ASP.NET Core 10.0 hosting. HostForLIFE is the leading provider of Windows hosting and affordable ASP.NET Core , their servers are optimized for PHP web applications such as the latest ASP.NET Core 10.0 version. The performance and the uptime of the ASP.NET Core hosting service are excellent, and the features of the web hosting plan are even greater than what many hosting providers ask you to pay for. At HostForLIFE.eu, customers can also experience fast ASP.NET Core hosting. The company invested a lot of money to ensure the best and fastest performance of the datacenters, servers, network and other facilities. Its data centers are equipped with top equipment like cooling system, fire detection, high-speed Internet connection, and so on. That is why HostForLIFE.eu guarantees 99.9% uptime for ASP.NET Core . And the engineers do regular maintenance and monitoring works to assure its ASP.NET Core hosting are security and always up.